Introduction
AD ACL Scanner 4.5.0 In the complex and ever-evolving landscape of IT security, the integrity of Microsoft Active Directory (AD) is paramount. AD is the bedrock of identity and access management for countless enterprises, controlling user access to critical network resources. However, its inherent complexity, especially regarding permissions and access control lists (ACLs), can create hidden vulnerabilities and compliance gaps. Enter AD ACL Scanner 4.5.0, a specialized PC software tool designed to illuminate the shadows of your AD permission structure. This powerful utility empowers IT administrators, security auditors, and compliance officers to proactively discover, analyze, and remedify excessive or dangerous permissions, thereby fortifying their security posture against insider threats and external attacks.

Overview
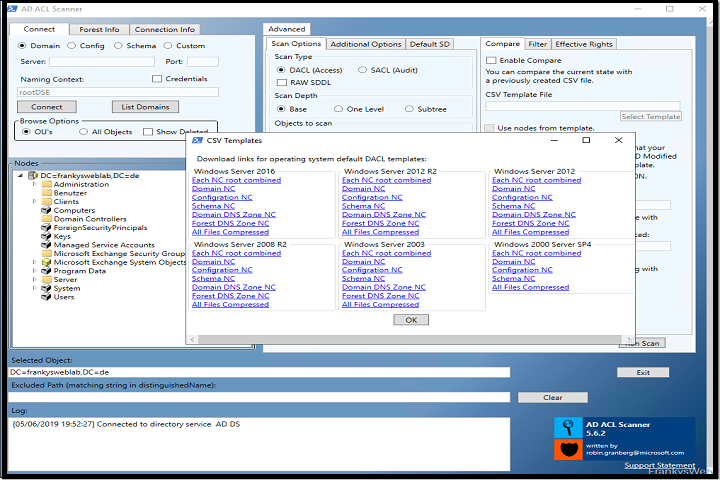
AD ACL Scanner 4.5.0 is a sophisticated, Windows-based auditing application developed to provide deep visibility into the permission inheritance and security descriptors of Active Directory objects. Moving beyond native tools like dsacls or the Active Directory Users and Computers (ADUC) snap-in, which offer limited, object-by-object views, AD ACL Scanner delivers a holistic, report-driven approach. It systematically scans domains, organizational units (OUs), groups, and users to map out every explicit and inherited permission. Version 4.5.0 represents a mature release, incorporating years of feedback to offer enhanced performance, more granular filtering, and comprehensive reporting capabilities, making it an indispensable tool for maintaining a least-privilege environment.
Description
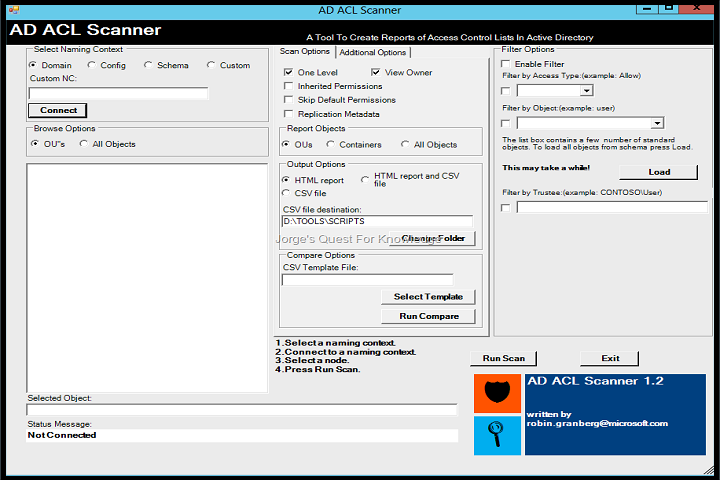
At its core, AD ACL Scanner 4.5.0 is a diagnostic and reporting engine for Active Directory security. It connects to a domain controller, enumerates objects based on user-defined criteria, and extracts their full ACL data. This data is then parsed, analyzed, and presented in an intuitive interface that highlights potential security risks.
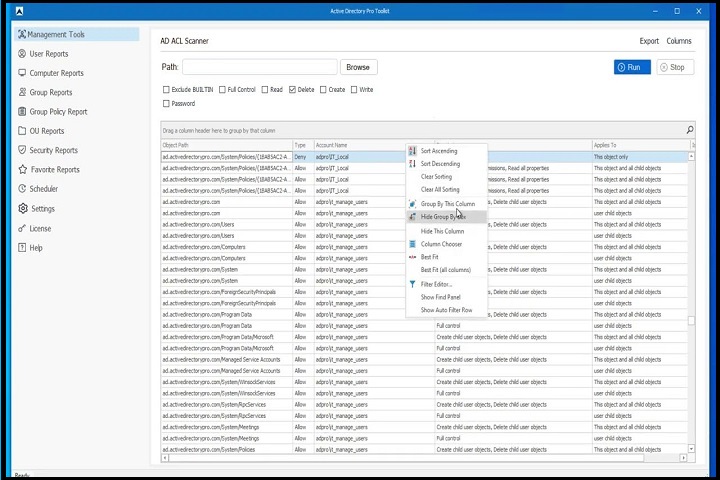
The software categorizes permissions in a clear, hierarchical manner, showing not just what permissions are set, but who has them (whether users, groups, or well-known security principals), and where they are applied from (directly on the object or inherited from a parent). Its primary function is to answer critical questions: “Who can reset a domain admin’s password?” “Which users have excessive write permissions to sensitive OUs?” “Where are ‘Everyone’ or ‘Authenticated Users’ groups granted modify rights?”
Version 4.5.0 enhances this further with improved search filters, allowing administrators to zero in on specific security identifiers (SIDs), permission types (like WriteProperty, ExtendedRight, or GenericAll), and risky permission combinations. The result is a actionable intelligence that turns the opaque world of AD ACLs into a clear roadmap for security hardening.
Key Features
-
Comprehensive ACL Enumeration: Scans and lists all permissions (Allow/Deny) on AD objects including domains, OUs, users, groups, computers, and GPOs, detailing trustee, permission type, and inheritance flags.
-
Advanced Risk Analysis & Highlighting: Automatically flags high-risk permissions, such as:
-
GenericAll(full control) grants on user or group objects. -
WriteMemberorAddMemberon privileged groups like Domain Admins, Enterprise Admins, or Schema Admins. -
Dangerous extended rights like
ForceChangePasswordorDS-Replication-Get-Changes-All. -
Permissions assigned to non-standard or poorly secured principals.
-
-
Powerful Search and Filtering (v4.5.0 Enhanced): New and improved filters enable precise audits. Search for permissions by trustee name, SID, permission type, or object type. Create complex queries like “Show all objects where ‘Authenticated Users’ have any Write permission.”
-
Inheritance Mapping and Visualization: Clearly displays the inheritance chain, showing whether a permission is applied directly or inherited from a parent container. This is crucial for understanding the source of a permission and where to make changes to effectively remove it.
-
Comparison and Change Tracking: Ability to save scan results as baseline snapshots and compare them with future scans. This feature is vital for change management, compliance audits, and verifying that security cleanup efforts have been successful.
-
Detailed Export and Reporting: Export scan results in various formats including HTML, PDF, CSV, and XML. Generate ready-to-present reports for stakeholders or detailed datasets for further analysis in tools like Microsoft Excel or Power BI.
-
Offline Analysis Capability: Can connect to live domains or load saved data files for offline analysis, allowing security professionals to conduct audits without impacting production environments or from a secure, isolated workstation.
-
User-Friendly Interface: Presents complex ACL data in a structured, multi-pane interface that separates object tree, permission list, and permission details, significantly reducing the learning curve compared to command-line alternatives.
How To Install
Installing AD ACL Scanner 4.5.0 is a straightforward process:
-
Download: Obtain the installation package (typically an MSI or EXE file) from the (heropcs.net).
-
Prerequisites: Ensure the target PC has the appropriate .NET Framework runtime installed (see System Requirements).
-
Run Installer: Execute the installer with administrative privileges. Right-click the installer file and select “Run as administrator.”
-
Setup Wizard: Follow the on-screen setup wizard. You can typically accept the default installation path and settings.
-
Complete Installation: Click ‘Install’ and allow the process to complete. Launch the application from the Start Menu or desktop shortcut upon finishing.
-
Initial Configuration: Upon first run, you may need to enter domain credentials with sufficient read access to the Active Directory you wish to scan. It is recommended to use a dedicated audit account with read-only rights for security best practices.
System Requirements
To run AD ACL Scanner 4.5.0 effectively, your PC should meet the following requirements:
-
Operating System: Windows 10, Windows 11, Windows Server 2012 R2, 2016, 2019, or 2022 (64-bit versions recommended).
-
.NET Framework: Version 4.7.2 or higher. Later versions of Windows include this by default; it may be downloaded separately if needed.
-
Processor: 1 GHz or faster 64-bit (x64) processor.
-
Memory (RAM): Minimum 2 GB RAM (4 GB or more recommended for scanning large, complex domains).
-
Hard Disk Space: 50 MB for installation, plus additional space for storing report and snapshot files.
-
Network: Network connectivity to a domain controller in the target Active Directory forest.
-
Permissions: An Active Directory user account with at least read access to the directory objects you intend to scan. For a full audit, domain-wide read rights are required. The application itself does not require local administrator rights on the PC it runs on, unless installed in a protected directory.

